Security Scan
Security Scan provides automated vulnerability assessment and security checks to identify potential risks and security issues on your server.
Security Scan Overview
URL: /admin/security-scan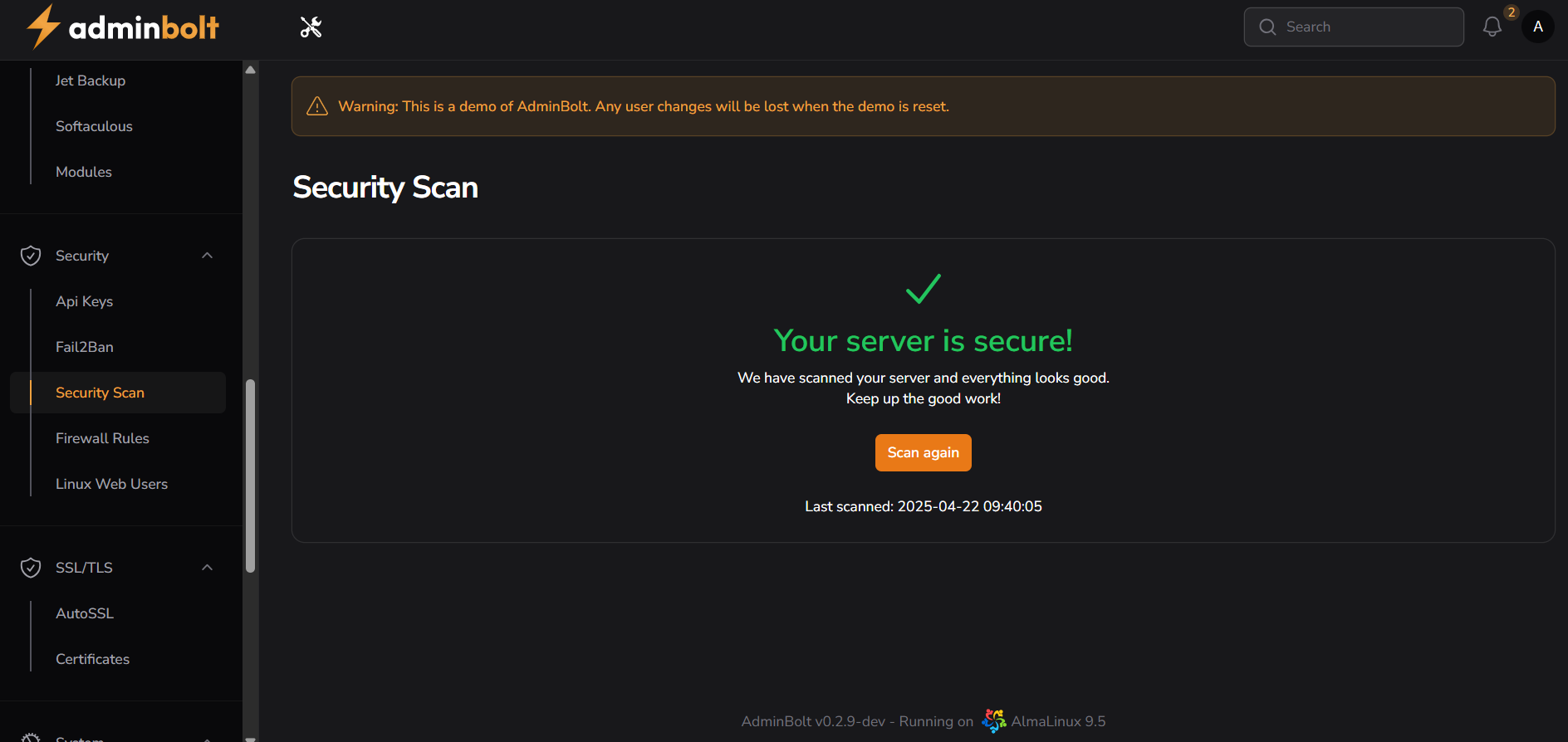
Interface Elements
Main Display Area
- Security Status Indicator
- Green checkmark for secure status
- Color-coded visual indicators
- Clear message display
Status Message
- "Your server is secure!"
- Prominent success message
- Positive reinforcement for good security
- Clear system health indicator
Scan Results
- Status Description
- "We have scanned your server and everything looks good."
- Clear explanation of scan results
- Encouraging message: "Keep up the good work!"
Action Controls
- Scan Again Button
- Orange button for quick re-scan
- Initiates new security assessment
- On-demand security check capability
Scan Information
- Last Scanned Timestamp
- Format: YYYY-MM-DD HH:MM:SS
- Example: "Last scanned: 2025-04-22 09:40:05"
- Provides scan history reference
Feature Functionality
Automated Security Assessment
- Comprehensive vulnerability scanning
- Real-time system analysis
- Instant status reporting
- Continuous security monitoring
Scan Components
- System configuration checks
- Vulnerability detection
- Security policy compliance
- Access control verification
Navigation Integration
Security Menu Structure
- Security → Security Scan
- Quick access from main navigation
- Integrated with other security tools
Related Features
- API Keys
- Fail2Ban
- Firewall Rules
- Linux Web Users
- SSL/TLS Management
Status Indicators
Secure Status
- Green checkmark icon
- "Your server is secure!" message
- Positive reinforcement display
Issue Detection
- Color-coded warnings
- Detailed issue descriptions
- Remediation recommendations
Best Practices
Regular Scanning
- Schedule routine security checks
- Monitor scan history
- Address issues promptly
- Document security status
Response Protocol
- Review scan results carefully
- Implement recommended fixes
- Re-scan after changes
- Maintain security records
Troubleshooting
Common Scenarios
- Unexpected security warnings
- Scan failures or errors
- Persistent vulnerabilities
Resolution Steps
- Review scan details
- Implement suggested fixes
- Re-run security scan
- Verify issue resolution
- Document changes made
System Integration
Complementary Tools
- Works with Fail2Ban
- Complements Firewall Rules
- Integrates with SSL management
- Supports Linux User security
Automated Protection
- Continuous monitoring
- Real-time threat detection
- Proactive security measures
- Automated reporting
Management Benefits
- Centralized security assessment
- Automated vulnerability detection
- Real-time security status
- One-click security scanning
- Historical scan records
- Proactive risk management
- Comprehensive system analysis
- Simplified security maintenance
System Requirements
Prerequisites
- Active adminbolt subscription
- Security module enabled
- Proper system permissions
- Network connectivity
Technical Specifications
- Automated scanning engine
- Real-time analysis
- Comprehensive reporting
- Low resource impact
Maintenance Guidelines
Regular Tasks
- Perform weekly scans
- Review scan results
- Address identified issues
- Document security changes
Best Practices
- Keep system updated
- Monitor scan frequency
- Respond to warnings promptly
- Maintain security logs
Management Benefits
- Centralized security assessment
- Automated vulnerability detection
- Real-time security status
- One-click security scanning
- Historical scan records
- Proactive risk management
- Comprehensive system analysis
- Simplified security maintenance